

Volcano is a client for the Dark Internet Mail Environment (DIME) as well as the existing email
ecosystem (POP, IMAP, and SMTP). Available cross-platform and on desktop and mobile, Volcano allows you to send
and receive secure mail without any extra work while also alerting you to possible security threats. It is the
ultimate privacy tool, completely free, and works just like the email clients you already use.
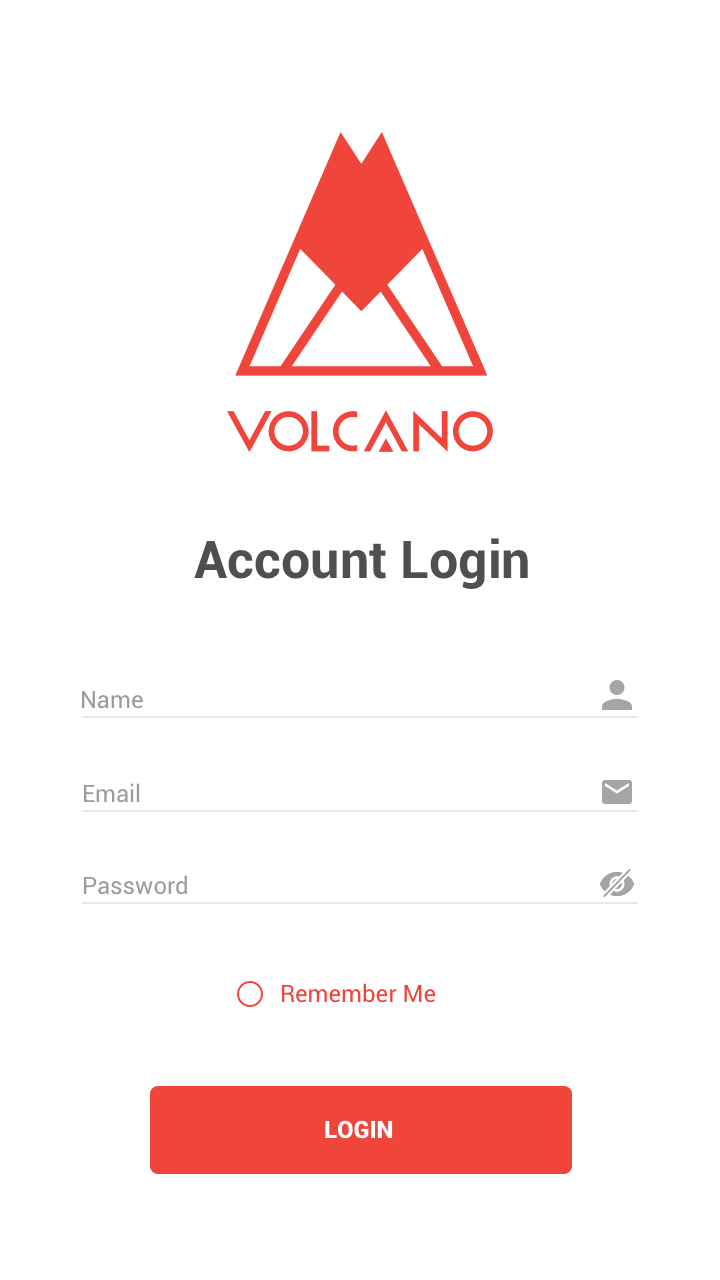
The Volcano mobile clients are in the very early stages of development. Below are a few mockups of what Volcano may look like.

Lavabit relaunches, releasing DIME and Magma to the world. DIME provides multiple modes of security (Trustful, Cautious, & Paranoid) and is radically different from any other encrypted platform, solving security problems others neglect. DIME is the only automated, federated, encryption standard designed to work with different service providers while minimizing the leakage of metadata without a centralized authority. DIME is end-to-end secure, yet flexible enough to allow users to continue using their email without a Ph.D. in cryptology.
Developed by Lavabit, DIME is an open source secure end-to-end communications platform for asynchronous messaging across the Internet. DIME follows in the footsteps of innovative email protocols, but takes advantage of the lessons learned during the 20-year history of PGP based encrypted communication. DIME is the technological evolution over current standards, OpenPGP and S/MIME, which are both difficult to deploy and only narrowly adopted. Recent revelations regarding surveillance have pushed OpenPGP and S/MIME to the forefront, but these standards simply can’t address the current privacy crisis because they don’t provide automatic encryption or protect metadata. By encrypting all facets of an email transmission (body, metadata and transport layer), DIME guarantees the security of users and the least amount of information leakage possible. A security first design, DIME solves problems that plague legacy standards and combines the best of current technologies into a complete system that gives users the greatest protection possible without sacrificing functionality.
To accommodate the radically different user needs, DIME operates in 3 account modes: Trustful, Cautious & Paranoid. Each mode represents a unique point in the security-functionality spectrum and determines how accounts operate. The difference between each mode is based on where message encryption (or decryption) occurs and where the user’s private key is stored.
For users who want a more secure email environment, but require the ability to use existing email software, we created Trustful mode. As the name suggests, Trustful mode requires users to "trust" the server to manage encryption. This mode ensures an ease of use, as users do not need to worry about technical requirements, or incompatibility with existing email clients. We envision Trustful mode as the mode of choice for businesses, which have regulatory requirements, data retention practices, and unique needs like escrow keys. Lavabit’s free and open source server, Magma, supports these users.
In Trustful mode, your key is within our server's memory only while you are logged into the server. The server performs the encryption on your behalf, and as such, you must trust that the server will not be rewritten in such a way that it captures your password, or peeks at your messages during processing. This magic black box mode is no different from many other encryption systems, which perform encryption automatically. The only difference is where the encryption takes place. The key question is whether you are comfortable trusting the implementation to function securely. If you feel that trusting our servers to perform the encryption is unacceptable, we offer other modes of operation, Cautious or Paranoid.
Cautious mode is the first level of true end-to-end encryption, your key, used for encryption is only in plaintext within the memory of your device, be it phone, laptop, desktop, or mainframe. The key is encrypted on this device and then transmitted through a secure tunnel to our servers, where it is safely stored in space designated specifically for your account.
If you have your account on one phone and decide to also install the client software onto your laptop, when you log into the system your cautious mode client can request the encrypted key from the server. Then on your laptop, using your passphrase, the client will be able to decrypt the key, and allow the client software on your laptop to access your messages. Only on the devices you control does your key exist in a format that it can be "seen". We anticipate most users will want the privacy and security of Cautious mode as it ensures you don’t have to trust your provider without having to alter the way you access your email. Users who believe they face a higher threat level and don't want a key to exist anywhere in any format except on devices where they maintain ABSOLUTE technical control may prefer Paranoid mode.
Paranoid mode is our most advanced and ultimate security mode. In Paranoid mode, your key never transmits anywhere; You maintain ABSOLUTE control. It is up to the user to move their key to any new device. If you create the original key within client software and wish to also use it on your phone, you must devise a secure method to move your key. This will allow you to export it to a file securely and encrypted. You can use a data cable or your own trusted digital method to copy the key to your new device. You can use a device to communicate for a period and then destroy the key or device, without a copy of the key stored. This renders all communication that that the key opened inaccessible from that point on. Paranoid mode is ultra-secure, however, requires technical proficiency in user key management.
Volcano is in very early development and there are currently no available downloads.
Volcano's source code is available on Github, and anyone who wishes to contribute code or submit bug reports is welcome to do so.
Changes, fixes, or updates to the Volcano codebase can be submitted via pull requests on the
Github repository against the develop branch.
Please make sure your code follows the preferred programming style for this project.
Bug reports may be submitted as issues on the Github repository. When submitting an issue,
make sure to include:
Donations of any amount support the development of Magma and help make the next-generation of private and secure email a reality. Thank you!